How do pirate groups prepare "crack" for games?

I remember the times when my friends and I would trade games on 5.25-inch floppy disks. Every copy was a treasure, but soon protections appeared that tried to prevent unauthorized copying. As early as the 1980s, there was a battle between developers, who introduced the first forms of copy protection, and young computer enthusiasts, called crackers, who wanted to show off their knowledge by circumventing these protections.
Floppy disks and the first cracks
The first forms of software protection were often quite simple, at least by today's standards. Game developers would implement various tricks on magnetic floppy disks to prevent easy copying, such as non-standard recording formats, bad sectors on the disk, or they would bundle physical aids (specially colored pages in the manual) with the game and require the player to enter a specific word from these materials when starting it. The legendary slogan of the era became "Don't Copy That Floppy", although it was rarely heeded by young enthusiasts, including me.
Despite the publishers' efforts, pirates quickly found ways to bypass these protections. Often, they would quickly find a place in the program where the game performed a check (for example, requiring the player to enter the correct word from the instructions) and release a crack – a modified version of the game that no longer contained such checks. As early as 1985, expert Laind Huntsman remarked that “no protection system will remain protected for more than a few months,” which says a lot about how ruthlessly effective the young hackers' efforts were.
The game Dungeon Master on the Amiga 500 console was one of the few examples at the time that lasted almost a year before crackers managed to find a workaround.
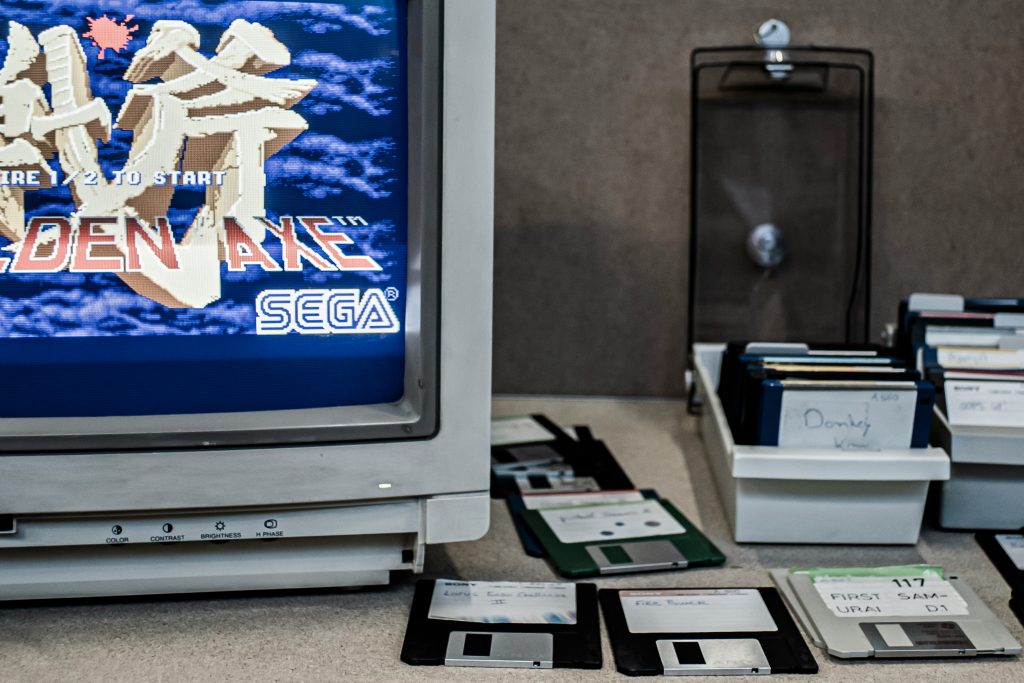
Already in the 1980s, pirate groups (so-called warez groups) developed, competing with each other to see who would be the first to "crack" a new game. These crackers operated from their parents' bedrooms or school computer labs and initially learned from their own trials and errors. Their motivation was not financial gain, but prestige. It was about demonstrating technical superiority and the challenge of breaking the protection itself. When they succeeded, they proudly embedded their name into the game in the form of a short animation or opening screen with the group's nickname. This gave rise to the famous cracktroys (a portmanteau of the words crack and intro), or short graphic introductions with music, logos and greetings that accompanied the pirated version of the game. This colorful digital graffiti was admired by other computer enthusiasts, and over time, even the beginnings of the demoscene – artistic programming separate from illegal piracy – developed from this.
TRIAD, Eagle Soft, Fairlight, Bonzai, Laser... These are the names of pirate groups that you may remember from your childhood.
Technically, crackers in the 1980s worked almost blindly. The first cracks were created through experimentation. They used hexadecimal editors or basic debuggers to examine the game's machine code and look for the part of the program that implemented the protection. Since they didn't have the source code, of course, they resorted to disassembling, or converting the machine code back into assembly language.
Sometimes they simply loaded the game into memory and used a so-called monitor – a program for viewing and editing memory contents, which could also display commands in assembly language. When they discovered a place where, for example, the game checked whether the floppy disk was original, this condition was removed or reversed. The most common method was to skip the unwanted check. In the machine code, they replaced the conditional jump instruction so that the program always continued executing the game, regardless of the check. This was achieved with minor corrections of a few bytes. They often inserted a useless NOP (no-operation) instruction instead of a jump or changed the machine code so that the program branch went in the right direction. Almost all classic cracks are based on this idea – to change a critical part of the game code so that the protection routine does not come into effect and the game runs unhindered. Anyone who mastered assembler could quickly become a successful cracker with a little practice in those days.
The 1990s were the years of the first personal computers and better protections
As the 1990s entered, the gaming world changed. Personal computers (PCs) became the popular gaming platform, and games grew in size. Instead of floppy disks, games began to spread on CD-ROM media, which brought new forms of protection. One of them was the simple CD Check. The game checked during startup whether the original CD was in the drive. Pirates responded with so-called “No-CD” cracks, which repaired the game’s executable file so that this media check was no longer necessary. One of the more popular sites where you could get crack files at the time was gamecopyworld.com, which still exists in exactly the same form as it did almost two decades ago. The process was so easy that anyone could play pirated games if they knew how to copy and paste the crack.exe file.
At the same time, serial keys (product numbers) appeared, which the user had to enter during installation. These keys were the first attempt to tie the game to the legal buyer. But even here, pirates quickly found another way. Instead of fixing the program, they sometimes preferred to decipher the algorithm for valid serial numbers. This gave rise to keygens, small programs that could generate valid serial keys for a game or software. This required the cracker to decipher the part of the code that checked the key and determine the mathematical formula or logic for the correct key.
Keygens were often little works of art. In addition to their basic function (generating working keys), they also had an aesthetic touch. Many had interesting graphic effects and 8-bit music, like a kind of mini-demoscene products. They were written in various languages, from assembler to C++, depending on the author.
With the spread of the Internet in the late 1990s, a global piracy infrastructure was also created. Through BBS servers (bulletin board systems) and early Internet channels (FTP servers, IRC), cracks and pirated game releases spread even faster and wider.
Pirate groups like Razor 1911, Skid Row, Reloaded and others have become almost legendary names among gamers. Hundreds of thousands of people around the world have seen their signature on their illegally acquired games. Although these groups operated underground, they created a reputation and name for themselves comparable to a rock band in music circles. For many young gamers, these pirate groups were even bigger heroes than the game developers. I remember reading the NFO files (text files) that accompanied pirated releases. They were full of ASCII art, humorous messages and proud statements about who had successfully cracked the game. From them you could tell what kind of team was behind a particular product and how sophisticated the protection they had overcome was.
Protection techniques began to escalate during this period. In addition to simple checks of the legitimacy of the CD, publishers resorted to more robust solutions. Professional DRM libraries were emerging, such as SafeDisc (from Macrovision, around 1998) and SecuROM (under the auspices of Sony DADC). These protections incorporated special routines into the game's programming code that verified the presence of the original disc by looking for digital signatures or even physical irregularities that a copy could not recreate.
At first, these protections were relatively predictable to crackers. Developers didn't update them often, so it was believed that once a team figured out how the protection worked, they could write an automatic crack tool that removed the same protection for all subsequent games.
Of course, this did not last long. Towards the end of the decade and the beginning of the new millennium, protections became increasingly dynamic and complex. Publishers and companies that developed DRM realized that they had to constantly change the protections if they wanted to cause hackers headaches. So they updated SafeDisc/SecuROM with each major game, adding new layers of checks and also started using more aggressive approaches, such as encrypting parts of the code and compressing executable files (using so-called packers), which packaged the game in a kind of wrapper, making it harder to find the protection code.
Internet, DRM and increasingly difficult problems
A little over twenty years ago, we got faster internet and mass sharing of pirated files via networks like Napster, eDonkey, eMule, BitTorrent and the like. At the same time, game protections reached a new level of sophistication. The term DRM (digital rights management) appeared, which refers to a whole range of technologies for controlling the use of digital content. For PC games, this meant even stronger forms of protection that addressed not only the media (CD/DVD), but also the software itself. SafeDisc and SecuROM continued to develop, but alongside them, the infamous StarForce appeared – a Russian protection that was known as one of the toughest to crack in the first decade of the millennium.
StarForce gained an almost mythical status among gamers and pirates. It was implemented as a set of drivers in the system that penetrated deep into the operating system and controlled access to the drive and the game. Where SafeDisc, for example, only checked a few hidden sectors on a CD, StarForce did everything possible. From checking for read delays from the optical drive (which a disk image on a virtual drive could not easily recreate), to installing hidden drivers that prevented the game from running if it detected any suspicious interference. I remember that gamers complained that StarForce sometimes caused problems even on legal systems. It was a very invasive protection that slowed down systems and required Internet activation, which was something new at the time.
For crackers, the arrival of StarForce was a real challenge and perhaps the first serious threat to any game remaining uncracked for a long time. The first successful crack of StarForce protection was created only after many months of effort. The author of one of the first StarForce cracks needed several months of intensive analysis and programming to do so.
Some games equipped with StarForce (Ubisoft games and the like) circulated on the Internet in the form of a "disk image" that you had to mount with tools like Daemon Tools or Alcohol 120% and use special tricks to bypass the protection, such as booting from a specific IDE/SATA drive or turning off drives. There was a time when there was no simple crack available, but rather instructions on how to bypass StarForce with half-baked solutions. But over time, StarForce also declined.
How do crackers cope with such demanding DRM systems? The answer lies in increasingly sophisticated methods and tools for reverse engineering. Decades ago, code disassembly tools reigned supreme. SoftICE was very popular among crackers. It was replaced by OllyDbg. In addition to it, the legendary IDA Pro (Interactive Disassembler) became established, which, in combination with its “Hex-Rays decompiler” module, enabled in-depth static analysis. With it, you could convert machine code back into pseudo C code, which was very helpful in understanding complex protections.
The most commonly used tools by modern crackers are IDA Pro (now also open source Ghidra) for disassembly and analysis, and debuggers such as OllyDbg and its modern 64-bit successor x64dbg for dynamic program tracing. With their help, the cracker literally walks through the game's code, line by line, until he finds the part that performs the protection checks. There, he then intervenes in the code (usually in memory during debugging) and tests the changes to see if they remove the protection.
When it finds a minimal set of fixes that disable DRM (whether it's skipping the serial number check, disabling the disc presence check, or removing the trial version time limit), it writes these changes. A "patch" or a small program is created that will make the same changes to the original game for other users. This is the key part of the crack. The patch changes only a few bytes in the game's executable file, but these bytes determine whether the game will require authentication or run without restrictions. The advantage of patch cracks is that they are very small (only a few kilobytes), as they do not contain the entire game, but only a correction to the machine code in the places where the protection was.
Since DRM developers knew that crackers were gradually deciphering their schemes, between 2005 and 2010 they began to build more and more tricks into their protection code that made it more difficult to use the above-mentioned tools. Protections began to detect whether they were running inside a debugger (and in this case behave differently or not run at all). Self-detecting code appeared. The program checked its own code at hundreds of places to see if it had been modified, and if it detected a deviation, it would throw an error or silently disable some part of the game.
Techniques such as metamorphic code and polymorphic encryption became part of the DRM repertoire. For example, the security code changed slightly with each launch (making it difficult to identify), or it was deeply encrypted and decrypted only during operation, often using dynamic keys tied to the hardware.
Some DRMs literally locked the game in a kind of virtual machine (VM). The game program ran inside a controlled environment where every instruction was checked by another layer of software. Crackers had to first trick this virtual machine to get to the real game code.
Developers were constantly throwing logs under the feet of crackers. When they thought they had won, developers came up with new challenges, such as CRC checking, which made the game constantly check the integrity of files to detect if they had been modified. Or security developers deliberately built in fake traps, so that certain codes looked like they were key to protection, when in fact the real mechanism was hidden elsewhere.
Crackers responded by upgrading their approaches. For the most difficult protections, it was no longer enough to find a “single true/false condition”. Sometimes it was necessary to decipher the entire mechanism and write customized tools for it. For example, when the protection spread to thousands of places in the program, they wrote scripts that automatically combed the code and eliminated the protected parts. For example, one such tool circulated on private forums of the pirate scene twenty years ago. It was able to remove SecuROM protection from the .exe file, thereby restoring a “clean” version of the game without DRM. Of course, the authors of the protections changed their method soon after.
Interestingly, I've heard several times that during this period, cracks even made some games faster. Why? Because some protections caused a performance drop despite all the checks. Players reported that the pirated version of the game ran smoother than the legal one. This happened, for example, with the game Resident Evil Village (2021), where they found that the pirated edition without Capcom's DRM and Denuvo did not have the stuttering that plagued the original. The publisher later released a patch that improved performance. Of course, this does not mean that piracy benefits games, but it does point to an interesting side effect. Cracking sometimes also means removing ballast, which makes the game better optimized.
Did Denuvo win?
Around 2014, a new challenger appeared on the scene, promising publishers that it would finally put an end to piracy (at least on PC). The Austrian company introduced Denuvo Anti-Tamper. This was not a classic DRM protection in the sense of a standalone library, but rather an addition to existing protection (Steam's DRM, Origin ...), which acted as a layer against code counterfeiting.
Denuvo tied games to your computer's hardware and created unique keys. When you first launched the game, it tied itself to your configuration. Each copy of the game received a special token tied to your processor, graphics card, motherboard, etc., and the game was saturated with calls that checked this token. Denuvo's code was embedded in the game in so many places that it was almost impossible to remove the protection without breaking the game. Imagine some kind of virtuoso encryption and code interweaving, where the game's real functions and protection mechanisms overlap like a woven tablecloth. If you pull out one thread, the entire weaving can be destroyed.
The first Denuvo games (FIFA 15 and Dragon Age: Inquisition in 2014) were a tough nut to crack. It wasn't until late 2014 that Chinese piracy group 3DM announced that they had cracked Denuvo and would soon release a crack. And they did, but it took almost a month for just one game, while previously cracks were ready in a matter of days.
The leader of the 3DM group, known by the nickname Bird Sister, even stated in early 2016 that they were giving up on Just Cause 3 and that it might happen that “in a year or two there will be no more free-to-play games.” This statement echoed across piracy forums and torrent sites. Many interpreted it as an admission of defeat.
3DM then symbolically announced a one-year moratorium on cracking games to see if game sales would improve if pirates were not involved. Perhaps it was also a tactical retreat. At that time, European groups entered the scene, determined to show that any protection can be broken sooner or later.
The Italian group CPY (Conspiracy) became synonymous with successful Denuvo cracks in 2016-2018. They took up the baton where others gave up. For example, the game Assassin's Creed: Origins (2017), which used Denuvo in combination with VMProtect and Ubisoft's own Uplay protection (i.e. triple protection), collapsed after about three months of work. They spent three months working on this one game, which was previously unheard of, but they succeeded.
On the other hand, publishers were celebrating at the time. Denuvo gave them 90 days during which the game sold well because there was no pirated version. That was actually Denuvo's main selling point. They don't guarantee impenetrability forever, but if the protection can last the first few weeks or months when the biggest profits are made, it has served its purpose.
Crackers, however, did not throw a gun at corn. Denuvo turned out to be a tough nut to crack, but not an unbreakable one. By 2017, we had experienced an incredible turnaround. What had initially been impenetrable for almost a year was now falling within a few days or even hours. For example, South Park: The Fractured but Whole, Middle-earth: Shadow of War, Total War: Warhammer II and FIFA 18 were all cracked on the day of release in the fall of 2017. This was a huge blow to Denuvo and the publishers.
It turns out that the pirate groups have cracked the Austrian Enigma. They haven’t revealed how they did it, but they’ve apparently managed to automate or greatly speed up the process of breaking this protection. They’ve probably built their own advanced analytics platforms that can track the execution of the Denuvo code, perhaps even extract the decrypted game code from memory and “clean” it with Denuvo. If rumors from closed forums are to be believed, some versions of Denuvo have taken an approach where they “instrumented” the game at runtime, so to speak, by letting Denuvo decrypt parts of itself while you’re playing, and then capturing the discovered code and “patching” it back into the pirated edition. It sounds like science fiction, but given the speed of cracking that year, something like this almost certainly went on in the background.
Today, Denuvo is still present in many AAA games, but its reputation among gamers is quite shaky. Many hate it because it can cause performance issues and because it locks games to one device, while knowing that no protection is perfect in the long run. A new name has emerged on the scene: Empress – a freelance hacker (no one knows), who in 2020-2023 became notorious for cracking several successive versions of Denuvo on her own and unlocking games such as Resident Evil Village, Red Dead Redemption 2, Jedi: Survivor and more. In the manifestos accompanying her cracks, Empress wrote, among other things, that she “enjoys destroying Denuvo” and that she does this because she believes that DRM humiliates honest buyers. Her case illustrates the fine line between ethics and illegality. On the one hand, her actions are welcomed by the masses because they bring them games that sometimes work better, without online restrictions... but on the other hand, it is clear that this is a violation of the law and that her cracks also enable simple piracy (playing the game for free).
One of the paradoxes of the battle between DRM and crackers is that nothing is permanent. This is confirmed by the more than 40-year history of piracy. However, it is true that the time frame has changed considerably. Once upon a time, a crack followed the release of a game on the same evening, but today this protection is effective enough to keep pirates at bay for weeks, months, or even years.
But that's also why the nature of piracy has changed. It used to be about the rapid spread of the most popular games, but today the focus is perhaps more on archiving and preserving games for history. The cracker scene has grown tired of Denuvo (Empress recently retired), not because it can't be cracked, but because the process is long and uninteresting, and the game may lose relevance in the meantime. Many new games are thus pirated with a delay or not at all, until the publisher themselves remove Denuvo, which happens when they judge that sales have declined and that DRM is no longer needed. Many games have received an update a year or two after release that removed Denuvo, which is a tacit admission that DRM no longer makes sense.
Increasingly, pirates rely on hypervisor and offline activation techniques
The latest and most technically fascinating front in this war has moved even deeper into the heart of the hardware – to the Ring -1 level, where the hypervisor operates. While Denuvo and anti-cheat systems attempt to control the operating system at the kernel level (Ring 0), modern crackers use techniques that virtualize the entire operating system.
In this context, a cracker nicknamed Voices38 has recently gained prominence. He became famous for being able to crack demanding Denuvo games such as Dead Space Remake and Sonic Frontiers, while also providing support for Linux. His approach, and that of teams such as MKDEV and 0xZeOn, often involves using a hypervisor to invisibly observe the execution of code.
The technique is based on the use of hardware-assisted virtualization (Intel VT-x or AMD-V). Instead of a classic debugger, the cracker uses tools such as HyperDbg, which operate independently of the operating system APIs.
Because the debugger runs at a lower level than the game and DRM, Denuvo cannot detect it with standard anti-debug tricks. Through Extended Page Tables (EPT), a cracker can intercept memory accesses and modify code in real time without triggering security mechanisms. The hypervisor can "spoof" responses to the CPUID command or other hardware registers that Denuvo uses to generate the hardware ID.
However, Voices38 and others warn that this method is risky. Using hypervisor bypasses means that the user exposes their entire hardware and operating system to code that operates at the lowest possible level, opening the door to potential security holes that classic crackers did not know about.
So-called offline activations are also very popular through communities like Anti-Denuvo Sanctuary. Instead of finding ways to completely remove the protection, this community focuses on offline activation, which allows players to launch games without constantly being connected to platforms like Steam.
Their technical approach is based on the use of specialized emulators and license generators, which are publicly available on their GitHub repositories. The Steam Ticket Generator is a tool written in Rust that allows the creation of encrypted application tokens (EncryptedAppTicket). This token convinces Denuvo that the game has been officially activated on the user's hardware.
Goldberg Fork is a modified version of the Steam API emulator that, when combined with a generated token, allows you to play without launching the Steam client itself. Ubi-dbdata is a specialized emulator for Ubisoft's implementation of Denuvo, simulating the dbdata.dll file, thus allowing you to bypass their specific security checks.

Locks will always exist, but so will locksmiths.
The path from the first cracks on 8-bit computers to sophisticated interventions in Denuvo is long and full of stories of genius, perseverance, and revenge.
The war between them continues, somewhere in the hidden corners of the internet, away from the public eye, until perhaps one day the news will surface again that XYZ game was cracked on release day. At that time, the pirates will laugh while the publisher will be scratching their heads in anger. And the cycle will continue indefinitely.