With a quantum computer, you can get a private key in 45 minutes

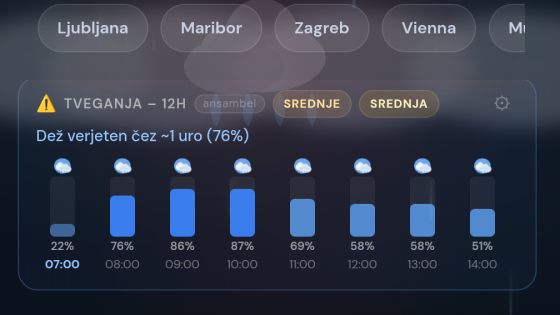
Lelli used a publicly available quantum computer in the cloud to derive the corresponding private key from the public key in about 45 minutes. He used a variation of Shor's algorithm that targets the elliptic curve discrete logarithm problem (ECDLP), the mathematical basis on which Bitcoin and Ethereum digital signatures are based.
This achievement represents a 512-fold increase in search space complexity compared to the previous record (6-bit key) set by Steve Tippeconnic in September 2025.
Is Bitcoin already at risk?
While this is a significant scientific advance, the current security of cryptocurrencies remains solid. The difference between the 15-bit and 256-bit keys that Bitcoin actually uses is enormous: a 15-bit key has only 32,768 possible combinations, while a 256-bit key has an unimaginably larger number of combinations (about $10^{77}). This would require millions of stable logical qubits.
Lelli only needed 27 physical qubits for the attack, while estimates for breaking a real 256-bit key range from 10,000 to 500,000 physical qubits, depending on the hardware architecture.
A warning for the future
Alex Pruden, CEO of Project Eleven, said the result is a reminder of the speed of progress. The fact that the attack was carried out on hardware in the cloud, rather than in a closed national laboratory, shows that the barriers to carrying out such attacks in practice are rapidly falling. Tech giants such as Google have already set a goal of becoming quantum-secure by 2029, suggesting the urgency of the transition to post-quantum cryptography.